16 November 2022
Updated: 23 November 2022
Symmetric Key Cryptography — What Is It and How Does It Work?
Table of contents
Table of contents
Data and information security are at the core of most technological innovations. People have always exchanged data and information and have done it on a global scale since the internet emerged.
To preserve the integrity of all exchanged data, finding ways to secure this information became necessary. ‘Encryption’ is an umbrella term used today to describe most mechanisms applied to securing electronic messages. One common form of data protection is symmetric key cryptography.
What Is Symmetric Cryptography?
Symmetric key cryptography (also called symmetric key encryption or private key cryptography) is an encryption technique that uses one key to encrypt and decrypt messages. It is an encryption method commonly used in banking and data storage applications to eliminate fraudulent charges, prevent identity theft, and protect stored data. Symmetric key cryptography uses mathematical functions to encrypt and decrypt messages. The method is “symmetric” because it uses a single key for encryption and decryption.
A key is a random series of binary digits or bits designed to scramble and unscramble transmitted data. The length and randomness of a key are major factors used to determine the strength of a symmetric encryption algorithm. The longer and more scrambled a key is, the more difficult it is for malicious parties to break the encryption by correctly guessing it.
A sender and a specified recipient have identical copies of the key, which remains secret to prevent outsiders from decrypting their messages. The sender uses the key to encrypt the message via an encryption algorithm known as a cipher, which converts plaintext to an encrypted version called “ciphertext.” The recipient then uses the same key to decrypt the message by converting the ciphertext back to human-readable plaintext. Anyone without the key would see the encrypted message as a series of random letters, numbers, and special characters, but would be unable to decode the message. In summary, symmetrical encryption works in 3 simple steps:
- A sender uses an encryption key to convert a plaintext message.
- This message is converted to ciphertext, making it unreadable to others.
- The recipient uses the same key to decrypt the message, converting it back to a readable form.
The Difference Between Symmetric and Asymmetric Encryption
Symmetric encryption is one of the two primary data encryption techniques in modern data storage and transmission systems. The other is asymmetric encryption, also called public key cryptography, which uses two different keys to encrypt and decrypt messages.
The beginning of asymmetric data encryption involves the creation of two keys, one of which is public and the other a private key. The public key is responsible for encryption, while decryption occurs with the private key. This process requires the intended recipient to provide the sender with their public key for data encryption, ensuring that decryption is only possible with the recipient’s private key.
Different types of encryption are better suited for specific situations. For example, symmetric encryption, which uses a single key, is more appropriate for data storage. On the other hand, asymmetric encryption is better for protecting information stored in databases to prevent data compromise or theft. This type of encryption is also the best option for financial transactions, especially for crypto exchanges.
Types of Symmetric Key Cryptography
There are two main types of symmetric key ciphers: block ciphers and stream ciphers. These ciphers operate different data encryption mechanisms and function in specific operating environments.
Block Ciphers
Block ciphers break down plaintext messages into blocks of predetermined sizes and convert them into ciphertext. Block ciphers usually encrypt block sizes of 64-bits and above and use keys of 56, 128, 192, or 256-bits. Two well-known implementations of block cipher include:
Data Encryption Standard (DES): DES was developed in the 1970s and is regarded as a legacy encryption standard. It used 56-bit keys and encrypted block sizes of 64 bits. Due to the short key length, DES was not very secure. However, it played a vital role in the evolution of cryptography.
Advanced Encryption Standard (AES): Cryptographers Joan Daemen and Vincent Rijmen designed the AES based on a principle called a substitution–permutation network, which produces a ciphertext block by applying alternating layers of mathematical operations. AES is an encryption algorithm used by the US government to encrypt classified information and is also common among tech companies such as Google, Mozilla, and Microsoft.
Stream Ciphers
A stream cipher uses a bit-by-bit method to convert the plaintext data into ciphertext by breaking down messages into single bits and converting them individually. This cipher uses a long stream of pseudorandom bits known as a ‘keystream,’ applied to each digit one at a time. The stream cipher uses an infinite number of pseudorandom digits per key and is also referred to as a ‘state cipher.’
For this form of encryption to remain secure, its pseudo-random cipher digits should be used only once so that they remain unpredictable. The encryption of each binary digit depends on the current state of the cipher, hence the name state cipher. RC4 (Rivest Cipher) is a common stream cipher widely used in software design.
Common Symmetric Encryption Algorithms
Some well-known symmetric encryption algorithms include:
- Advanced Encryption Standard (AES)
- Blowfish
- Twofish
- Rivest Cipher (RC4)
- Data Encryption Standard (DES)
Pros and Cons of Symmetric Key Cryptography
The following are common merits and demerits of symmetric key cryptography:
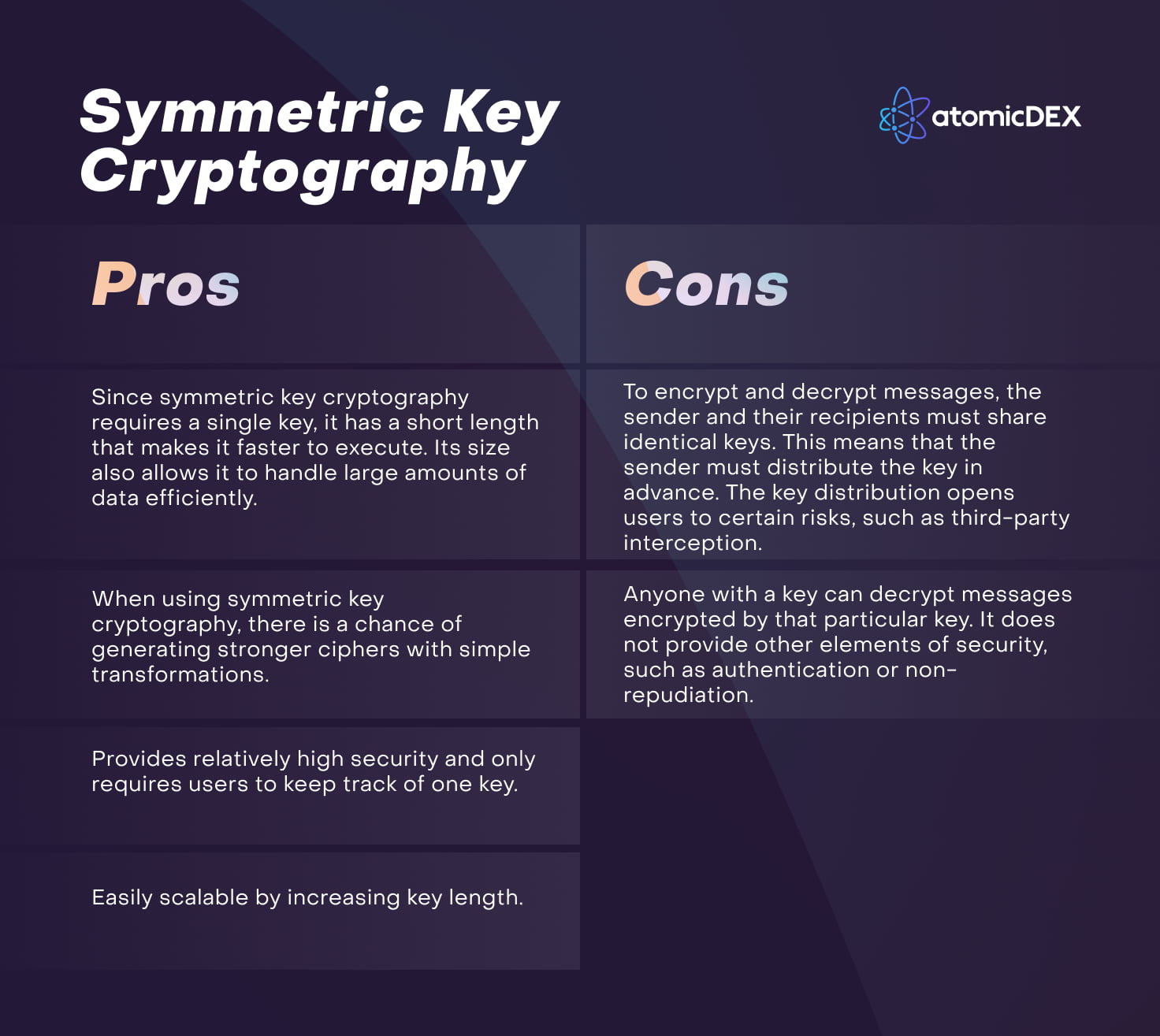
Securing Data Simply and Fast
Symmetric key cryptography is a relatively secure, fast, and simple method of encrypting and decrypting large quantities of data without straining servers. It has various applications across many sectors and is the standard encryption method used by established companies and governmental authorities worldwide.
The invention of symmetric key cryptography eventually led to the development of asymmetric key cryptography, which is the foundation of cryptocurrency payments and blockchain-based applications.
Hold and Trade Crypto On AtomicDEX
AtomicDEX is a non-custodial multi-coin wallet and atomic swap DEX. Store Bitcoin, Ethereum, Dogecoin, Zcash, Qtum, and many other coins in your own wallet. When you're ready to trade, AtomicDEX supports cross-chain swaps. Your keys, your coins.




